Postfix TLS
 Toores. Ehk seda pala võib täiendada.
Toores. Ehk seda pala võib täiendada.
Probleem: Sooviksime igalpoolt maailmast ühenduda kasutajanime ning parooli abil oma mailiserveriga ja saata läbi selle kirju. Samas kasutame palju ebaturvalisi võrke (wifi, lennujaam jms) seega peaks olema ühendus, mille üle käib suhtlus serveriga krüpteeritud.
Ehk siis startls loob serveriga krüpteeritud ühenduse ja autendib end läbi base64 krüpteeritud paroolide.
Genereerime base64 formaadis kasutajanime ning parooli
Postfixi seadistamine
Vajalik on lisada enda Postfixi seadistusele järgnevad read:
# lubame ligi vaid sisevõrgul ja sasli abil autentitud kasutajad smtpd_sender_restrictions = permit_mynetworks, permit_sasl_authenticated, smtpd_client_restrictions = permit_sasl_authenticated permit_mynetworks reject_unknown_client smtpd_recipient_restrictions = permit_mynetworks, permit_sasl_authenticated, reject_unauth_destination, smtpd_sasl_type = dovecot <- Autentimiseks kasutatakse dovecot imap serveri vahendeid smtpd_sasl_path = /var/spool/postfix/private/auth <- Dovecoti poolt loodud socket autentimiseks smtpd_sasl_auth_enable = yes smtpd_use_tls = yes smtp_use_tls = yes # linuxi puhul /dev/random tls_random_source = dev:/dev/urandom # Offer TLS encryption to clients smtpd_tls_security_level = may # krüptovõtmed smtpd_tls_key_file = /etc/ssl/smtpd.key smtpd_tls_cert_file = /etc/ssl/smtpd.crt # Only offer SMTP AUTH when talking over an encrypted connection smtpd_tls_auth_only = yes # Add some useful logging entries to track the use of TLS, you can omit this if desired smtpd_tls_loglevel = 1 # Add a header to mail received with TLS, can make debugging easier smtpd_tls_received_header = yes
If you truly do want to forbid unencrypted SMTP connections (I do this on ports 587 and 465), you'd want to use either "smtpd_tls_security_level = encrypt" (for STARTTLS, generally on port 587) or "smtpd_tls_wrappermode = yes" (for SSL encryption from the initial connection on, generally on port 465). You could also set "smtpd_tls_security_level = may" so that TLS encryption is offered but it's not mandatory (so-called opportunistic TLS).
Enabling the submission port Many ISPs block access to port 25, meaning that the above setup won't work for a lot of users. For this reason, port 587 is available, and is configured only for "outbound" relay access. You can do this easily in Postfix.
Edit /etc/postfix/master.cf and enable the submission port by uncommenting a couple of lines. Make sure not to mess up the whitespace - a logical line is continued by whitespace on the subsequent lines.
# We enforce the use of TLS, and override the client restrictions to only allow authenticated relaying submission inet n - - - - smtpd -o smtpd_tls_security_level=encrypt -o smtpd_sasl_auth_enable=yes -o smtpd_client_restrictions=permit_sasl_authenticated,reject
Kasutades IMAP serveriks Cyrust on mõistlik kasutada saslatuhd nimelist deemonit, mis näiteks kontrollib kasutajad PAMi kaudu.
Testimine
$ perl -MMIME::Base64 -e 'print encode_base64("kasutajanimi")'
$ perl -MMIME::Base64 -e 'print encode_base64("not.my.real.password")'
Kasutada saab ka http://base64-encoder-online.waraxe.us/ asuvat tasuta kodeerijat.
Ühendume openssl käsurea kliendi abil mailiserveriga:
$ openssl s_client -starttls smtp -crlf -connect mail.edu.ee:25
250 DSN helo test.eenet.ee 250 mail.edu.ee auth login 334 VXNlfm3hbdU6 dGVzdA== <- siia paneme kodeeritud kasutajanime 334 UGFzc1dwcAQ6 WAx3GVpcHpMQ== <- kodeeritud parool 235 2.7.0 Authentication successful
Edasi võib teostada juba tavalise kirjasaatmise protseduuri.
mail from: jj@eenet.ee 250 2.1.0 Ok rcpt to: jj@eenet.ee 250 2.1.5 Ok data 354 End data with <CR><LF>.<CR><LF> test . 250 2.0.0 Ok: queued as 60C1584BD0E11
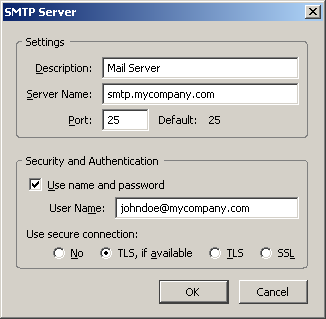
Thunderbirdis väljuvate kirjade seadistus:
http://wiki.centos.org/HowTos/postfix_sasl Ammendav juhend